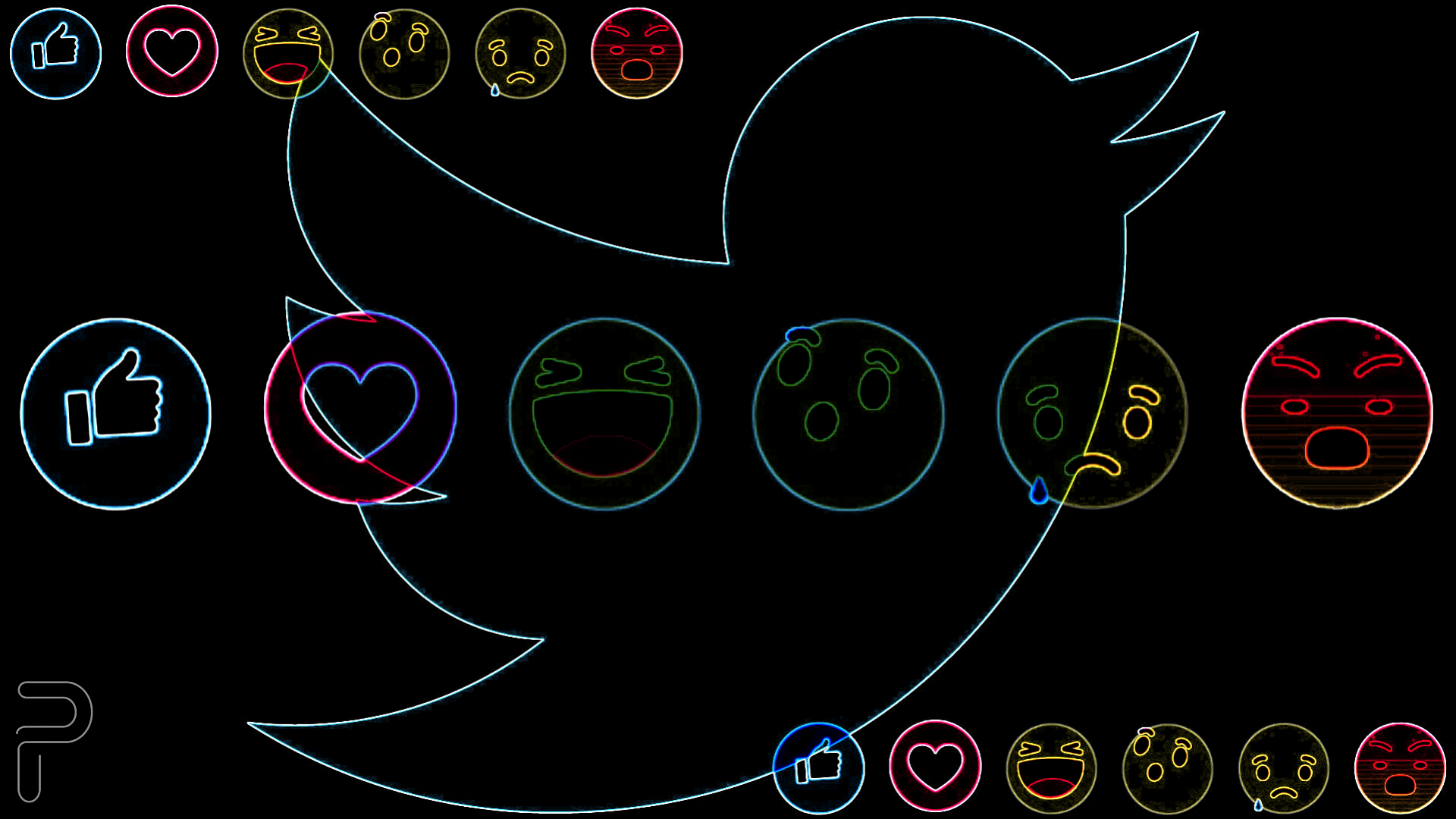
In today’s age where social media is ruling everybody’s life, emojis have become an important part of the conversation on these platforms. Looking at the importance of emojis, Twitter is working on an upgrade that will let users react to posts with emojis, just like Facebook. Twitter is taking some inspiration from Facebook to develop its social media reaction system so that users can easily react to tweets on the platform.
According to the screenshots shared by reverse engineering expert Jane Manchun Wong, the microblogging site could provide users with reactions such as Likes, Cheer, Hmm, Sad, and Haha to reply to different tweets.
These emojis and reactions will be similar to what available on Facebook and also to an extent on LinkedIn. It should also be noted that there are no signs of whether an angry emoji will be available on the platform or not, while as per the speculations, instead of angry emoji Twitter is providing users with a Humm reaction.
Twitter in its bid to exploring additional ways for people to express themselves in conversations is adding this new reaction feature on the platform. However, as of now, there is no word on when the website will release the new feature.